-
กฎหมายคุ้มครองข้อมูลไทย จะเดินตามโมเดลไหนดี: สหภาพยุโรป หรือ เอเปค?

EU General Data Protection Regulation จากปี 2016 กับ APEC Privacy Framework จากปี 2005 ถ้าไทยจะมีกฎหมายคุ้มครองข้อมูลส่วนบุคคล เราควรจะดูตัวอย่างจากกรอบใดเป็นหลัก?
-
ออกแบบหน่วยงานคุ้มครองข้อมูลที่มีประสิทธิภาพ: บทเรียนจากสหภาพยุโรป

วิธีปฏิบัติที่ดีที่สุด (best practices) สำหรับหน่วยงานคุ้มครองข้อมูล (Data Protection Authority) สรุปจากรายงาน Data Protection in the European Union: the role of National Data Protection Authorities ของสหภาพยุโรป
-
Hacking Team RCS กับการดู “ข้อมูลเข้ารหัส” โดยไม่ต้องถอดรหัส
RCS ไม่ใช่อุปกรณ์หรือระบบถอดรหัสการสื่อสาร แต่ทำงานโดยไปฝังตัวที่เครื่องปลายทาง เพื่ออ่านข้อมูลที่เครื่องเป้าหมายก่อนจะถูกเข้ารหัสและส่งออกไป และอ่านข้อมูลหลังเครื่องเป้าหมายได้รับและถอดรหัส / เมื่อ RCS เข้าควบคุมเครื่องได้แล้ว ก็แน่นอนว่าจะสามารถดูข้อมูลในเครื่องได้ด้วย Citizen Lab พบหลักฐานว่าระบบนี้ถูกใช้ในหลายประเทศ
-
ออกแบบอำนาจ: อ่านโครงสร้างคณะกรรมการในกฎหมายไทย
คำถามที่อยากค้นหาคือ เราจะดูตรงไหนได้บ้าง ว่าคณะกรรมการหนึ่งๆ มีกระบวนการสรรหาที่อย่างเหมาะสม ไม่มีผลประโยชน์ทับซ้อน มีอิสระในการทำงาน มีอำนาจในการทำงาน และอำนาจนั้นมีกลไกตรวจสอบชัดเจน ก็เลยไปดูในกฎหมายว่าเขาออกแบบโครงสร้างอำนาจกันอย่างไร
-
ประวัติกฎหมายลงทะเบียนซิมใน 3 จังหวัดภาคใต้ (2548 – ยุคก่อนประกาศกสทช.)
ขอความร่วมมือจากคณะกรรมการกิจการโทรคมนาคม ออกกฎหมายควบคุมซิม ถ้าหากกทช.เห็นว่าทำไม่ได้ ให้ใช้ พ.ร.บ.ควบคุมโภคภัณฑ์ พ.ศ. 2495 ของกระทรวงพาณิชย์ ที่กำหนดให้รัฐสามารถควบคุมโภคภัณฑ์เพื่อสวัสดิภาพของประชาชนและความมั่นคงของประเทศ
-
Forensic Service Act 2016 and the protection of personal data
So, keeps your eyes on the Forensic Service Oversight Committee and the forensic data regulations that they going to make. We hope they are going to have public consultations for that.
-
Quick notes on Thailand’s new cybercrime law amendment (26 Apr 2016 rev)
Look at Section 14 (1) [online defamation], 14 (2) [“public safety”], 15 para. 3 [burden of proof to the intermediary], 17/1 [Settlement Commission], 18 (7) [investigative power to access encrypted data-at-rest], 20 (4) [Computer Data Screening Committee can block content that is totally legal], and 20 para. 5 [will be used to circumvent data-in-transit encryption].
-
“ข้อยกเว้น” ที่อาจทำลายหลักการของร่างกฎหมายคุ้มครองข้อมูลส่วนบุคคลลงไปทั้งฉบับ #ไร้ค่า
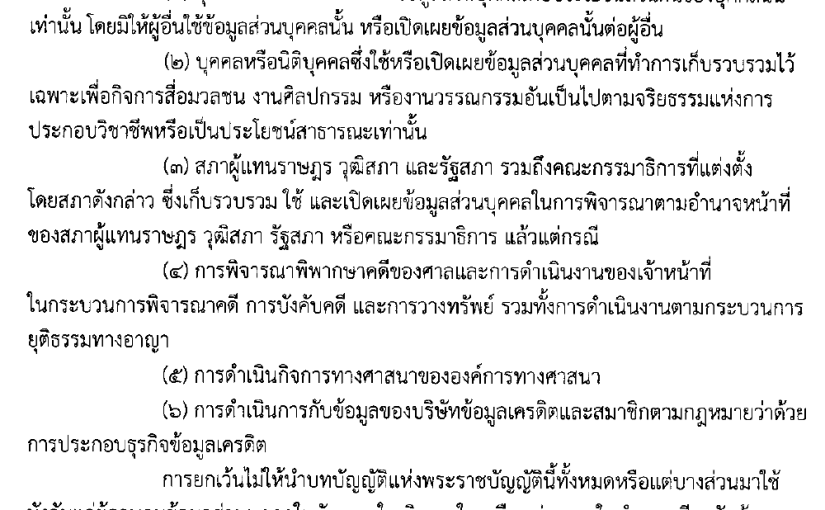
อ่านข้อยกเว้นในร่างพ.ร.บ.คุ้มครองข้อมูลส่วนบุคคล มองคดีศาลยุติธรรมแห่งสหภาพยุโรปตัดสินว่าข้อตกลง “Safe Habour” ระหว่างสหรัฐกับอียูเป็นโมฆะ แล้วเตือนใจตัวเองว่า ระวังอย่าให้ “ข้อยกเว้น” มาทำลายหลักการการคุ้มครองเป็นการทั่วไป ไม่อย่างนั้นมีกฎหมายไปก็เหมือนไม่มี #ไร้ค่า
-
Person API ขุดประกอบประวัติบุคคลจากอินเทอร์เน็ต
ความสามารถอันนึงของ Cobook และซอฟต์แวร์คล้ายๆ กัน อย่างตัว Contacts ของ Gmail ก็คือ มันสามารถ “merge” หรือรวมที่อยู่ติดต่อที่ซ้ำๆ กันให้มาเป็นอันเดียวได้ เช่น คนๆ นึงอาจจะมีมีหลายเบอร์โทร มีอีเมล มีทวิตเตอร์ มี LinkedIn มีบัญชีโซเชียลมีเดียอื่นๆ บางบัญชีใช้ชื่อจริง บางบัญชีเป็นชื่อเล่น ซอฟต์แวร์พวกนี้มันช่วยรวมทั้งหมดให้มาอยู่ในระเบียนเดียวกันได้ จะได้จัดการและค้นหาได้ง่ายๆ แล้วมันส่งผลกระทบอะไรกับสิทธิของผู้ใช้เน็ตอย่างเราไหม?